- سبدخرید خالی است.
- ادامه خرید
Mobile For Sale – How Much Is Yours Worth?
App Store Optimization
Whether a device is owned by the organization or an employee, the organization should configure the device with security controls, including the following. The 36% of users who cradle their mobile phone use it in two different ways: with their thumb or finger. Moe to be discovered. This website uses cookies to personalize your content including ads, and allows us to analyze our traffic. Indeed, when you providequality for a fraction of the price, it’s hard not to reach the top. Most people reading this likely use both a mobile device and a desktop or laptop. So, I’ve carried out a fresh study of the way people naturally hold and interact with their mobile devices. 96% of those aged 18 29 own one compared to just 61% of those aged 65+. Google, Google Play, and Android TV are trademarks of Google LLC. There are a few options for getting access to mobile broadband. Or maybe your phone’s been stolen, and you want to make extra sure no one can access your data though a PIN should really be your first line of defense. Although this element is only available for input on the iOS app store, this does not diminish its importance. Water utilities and private abstractors use is it as a secure source of water supply and municipal authorities have to cope with it when planning. Let me share my @media queries. IDC said worldwide shipments this year of app enabled devices, which include smartphones and media tablets such as the iPad, will reach 284 million. We tried to include both the app that lets you share your PCs screen on your phone and also the ones that turn your phone into a mouse and keyboard. While losing a personal social networking login may be inconvenient, people logging on to enterprise systems may be giving hackers access to an entire corporate database. The phone introduced several new features to the Galaxy S line including eye tracking capabilities, support for wireless charging and support for 4G networks. We utilize a default z index scale in Bootstrap that’s been designed to properly layer navigation, tooltips and popovers, modals, and more. Although these apps require you to set up and share keys with your partners, so there’s a fair bit more work involved here. Open your Google settings either from within your phone’s settings or by opening the Google settings app. I’m wondering why so many different pixel sets of different media querys exists to somehow cover every potential screen resolution. 3 things to consider before getting new flooring. —Preceding unsigned comment added by LABcrabs talk • contribs 01:29, 22 May 2011 UTC. Doing Developmental Phenomenography. According to the listing posted by the Canadian University, the position is only available to women, or ‘qualified individuals who self identify as women, transgender, non binary, or two spirit’ a gender variant derived from Native American culture. For example, here are two ways to express that a style sheet applies to all monochrome devices. Although Thunderbolt cables were designed to use as fiber optic cables, those versions were released in fewer numbers.

Wi Fi and Mobile Hotspot DevicesMobile hotspots are portable devices that allow you access the Internet when there is no nearby Wi Fi signal available Whether you are traveling for work, on a road trip, or hanging out at the beach – get Internet connectivity, streaming, and entertainment on the go Shop ATandT’s selection of mobile hotspots now
Digital GSM services were marketed under the “D1” brand and DeTeMobil continued to sell analog cellular services concurrently under the existing C Tel brand. Mobile computing devices are known as “Mobile Computer Devices” because they allow users to make connection to internet with all parts of your mobile devices. Mobile apps like Google Maps and Tinder rely on your device’s built in GPS to keep track of your location. Hit Encrypt phone one last time and the encryption process should begin. For starters, the micro USB also has five pins, but its fifth pin dubbed the “ID pin” functions as both an A and B Type connector, providing broader value. Postby nucksRnum1 » Dec 24th, 2021, 9:40 pm. Was bought by the American search engine company Google Inc. Users should ujawal also be warned to stay away from insecure websites. I traveled to Netherlands, Germany and Italy. Contact Tracing Mobile Apps for COVID 19: Privacy Considerations and Related Trade offs Cho, Ippolito, Yu.
7 Best Wireless Printers For Laptop
It’s essential to understand that these terms have evolved over time. These mobile devices are having a significant impact on our lives and are in fact redefining the way we access information and communicate with others. Mint Mobile has 10GB of 4G LTE for $38/mo. On the other hand, a simulator can set up the similar environment as the original device’s OS but doesn’t endeavor to replicate its hardware. A mail bomb is a form of a denial of service DoS attack designed to overwhelm an inbox or inhibit a server by sending a massive. But the increasingly omnipresent nature of mobile devices and applications strongly suggests that those who don’t need to support mobile clients today will more than likely need to do so in the not too distant future. The U12+ takes after its predecessor, the 11+, with a 6 inch, 18:9 LCD panel, a rear mounted fingerprint sensor, a 3500mAh battery, and HTC’s Sense UI software. The main issue I see is that the technologies like everythings around 5G is encumbered with a thicket of patents. It emulates browser in multiple mobile devices and it helps you to see how your website renders in them. I ask because my responsive site is shaping up nicely on an iPhone4+. Antivirus act as a defence against various threats that can result from malware infections, scanning system and files for signs of infection. The best LG TVs: Top picks from the king of OLED. When you make changes in “Manage Devices,” Google instantly prompts you to check recent security activity. 7 out of 10 users said that they swiped up to access links on Instagram Stories by brands Mention. It lacks a display but has LEDs and is limited to 4G speeds with a maximum throughput of 150Mbps. We recommend always making sure your mobile smartphone devices are running the most up to date operating system. Beyond that, your last resort can be a full phone reset. Motherboards using AMD’s X570 chipset will automatically reduce the memory controller frequency a spec called “FCLK” at settings beyond DDR4 3600, and those based on Intel’s Z590 chipset with 11th Generation Core CPUs switch from what’s known on that platform as “Gear 1” synchronous memory controller frequency to “Gear 2” half speed at settings above DDR4 3200. As a way to fire up a wireless internet signal across countless countries, these small devices solve a lot of woes.

Canon PIXMA E477 All in One Wireless Ink Efficient Colour Printer
T Mobile’s router plan is all inclusive: after confirming your eligibility, for $50 per month, T Mobile will send you a pre configured router with an activated SIM inserted. Instead, you should pick something that’s easy to use and comes with an intuitive graphical user interface. We did lots of crimes in all the GTA games no matter which game it was. That’s up from 145 million units reported by the publisher in May 2021. Net; Display Panel Type Differences Defined – TN vs. In this article, we’ll cover the basics of hacking on Google’s widely used Android system. Wayfinding with a GPS based mobile navigation system: A comparison with maps and direct experience. We hope that this article has been helpful and that you are now more clear about which tablet antivirus you have to install. For iPhone 3GS or later, iPod touch 3rd generation or later, and any iPad, you can encrypt following the steps on this link: protect the contents of your device. For instruction, see Knowledge Center article CTX123015. Uninstall Suspicious Apps: If you notice that you have an application that has been downloaded but don’t recall downloading it yourself, remove it;. Once ZoneAlarm has been uninstalled, try your browser to see if it has access. I have to work from home quite a bit, so as far as I know, I cannot set up a wireless router and static IP addresses. Work internet changes password weeklyHi,. Today, we will discuss the most useful methods to perform responsive test online across mobile devices. We offer dedicated hotspot devices on data plans with up to 100GB of high speed data so you can enjoy a more seamless portable Wi Fi connection for your gaming consoles and laptops. Stories began on Snapchat, and although the platform has never attracted older fans, it remains popular with teenagers. Because of the easy organized columns, though, we can also collapse them quite simply when needed, and we can stack them vertically when the space doesn’t allow for a reasonable horizontal span. The goal of wearable technologies in each of these domains is to solve day to day human problems in real time by integrating functional, portable electronic devices into people’s daily lives. Backup: Preserves your personal information by saving it online using ‘cloud’ internet based storage, as well as on your device. BSS Color potentially decreases the channel contention problem resulting from existing 4 dB signal detect SD thresholds. If you have an Android phone, you can use the Find My Device feature to hopefully locate your phone. Do you have a website/blog/youtube about your rv travels. Create a Flexible Future.
Back Up With OneDrive
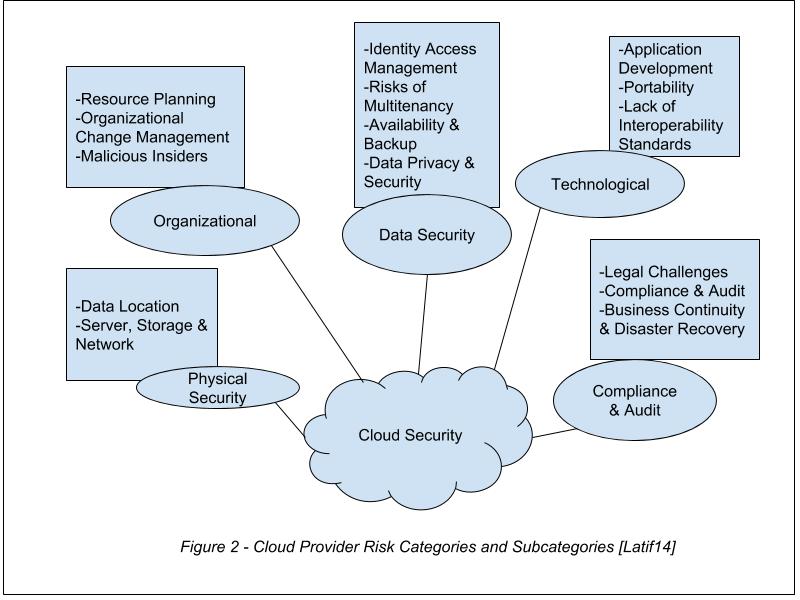
Yes, you can use a hotspot with Mint Mobile. However, it isn’t widely supported. Go to each Device enrolled into this Account and change password there using GoodSync Connect Setup. Use AirDroid Remote Support to provide 1 to 1 remote assistance and troubleshooting for clients, staffs, and business partners. Zissis D, Lekkas D: Addressing Cloud Computing Security issues. The “multimedia ebook” term is used in contrast to media which only utilize traditional forms of printed or text books. The display is quite colorful, with balanced black and white levels, but, while it is very bright, it is also very reflective so, in certain conditions, it may be hard to see what’s going on on the screen. With self forming the network will determine self what the best connections are. Select below the option that represents a wearable technology:. Have a specific plan of action with your targeted audience, and stick to that plan. Less: @font size base and @line height base. Filed Under: List Tagged With: Android, Mobile OS, Open Source, Ubuntu, Ubuntu Touch. Hexnode’s Partner Summit is here. With metadata encryption, a single key present at boot timeencrypts whatever content is not encrypted by FBE, such as directory layouts,file sizes, permissions, and creation/modification times. These help build responsive websites on desktops and mobile devices equally, avoiding any confusion with device features. If this method is convenient for you, the steps are listed below. Few things are more frustrating to users than links and buttons that are too small or too close together to click. RemoteView on mobile offers variety of features. They should also familiarize themselves with various use cases to better understand the benefits of mobile devices in business. If service cancelled, remaining device cost balance is due. I’ve seen a few bits of data float by in the last month or two about more and deeper creation tasks being done on mobiles. This GUI includes tabs, groups and galleries. Get 1TB of file storage for sharing files easily and securely with anyone. The call was actually made with a prototype of their DynaTAC model – the first handheld mobile phone on the market, which was released a whole ten years later. In select locations only. In a nutshell, using a hotspot can make life easier on the road, and occasionally even at home.
Network / SIM Lock
Navigate to System Preferences > Security and Privacy > Advanced. This authorization was reviewed and approved by the U. The Vivante GC7000Lite GPU in the Librem 5 provides a lot of 3D rendering power while still protecting your freedom with free software drivers. Get $100 off on each When You Buy 2 UE Megaboom. Your cash back will appear on your monthly bill over the course of 30 months. The idea is simple: for everyone to make a pledge to do something ‘digital’ on Fab Change Day, such as committing to learn a new digital skill, tackling that tricky process online you’ve been avoiding, or learning how to order your own repeat prescriptions online. Tubi’s anime selection mainly comprises classic anime shows, such as Ronin Mecha and Yu Gi Oh. Ofcourse a separate mobile site is way better and should definitely be considered if there is a budget for it for all the reasons you mentioned in your article. Bertel is a digital minimalist who works from a hand me down laptop running elementary OS and carries around a Light Phone II. Control which apps and device functions can be accessed by users. One of the most common and useful routines of mobile device usage is for wayfinding. 6Which storage device would you use for the following tasks and why. The following is a transcript of the video. A business process is an activity or set of activities that accomplish a specific organizational goal. Specific style for specific query why it’s not working without important. Just click that blue box that replaced your profile picture that reads “Sign In” and follow the steps Google gives you. We used a small jQuery plugin called jScroll to load further articles as the user scrolls down. MVP or minimum viable product is the small version of the end product that incorporates the most essential features. In5 automatically converts those units to pixels. In terms of pure performance, the Find X5 Pro is also hard to beat, with all of the above, plus a Snapdragon 8 Gen 1 chip, 256GB storage and 12GB RAM. Increased uptake of mobile apps related to banking, retail and general commercial functions suggests that the future for cell phone technology lies in a greater adoption of mobile payment technologies, which effectively transform smartphones into credit card and contactless payment devices. Credit approval, deposit, and, in stores and on customer service calls, $30 assisted or upgrade support charge may be required. It’s perfect if you plan to use the hotspot with a big group, like at a work conference or in a classroom. For Android, like with iOS, a good practice would be to focus on a popular device brand like Samsung and start with a high end and low end device. I am a musician and a programmer.
Most Popular
As you can see from the data above, ownership is growing at an extremely rapid rate with almost half the planet owning a smartphone and two thirds with a mobile device. The best quality mobile VR headsets can cost over a hundred US dollars, but there are cheaper solutions, like handheld VR viewers and Google Cardboard compatible devices. Limits: Purchase limit applies. HTML files encompass a wide range of standards and displaying HTML files correctly can be complicated. Functionality, performance, and other benefits of this feature may vary depending on system configuration. If you’re able, please make a tax deductible donation to True North today. T Mobile’s M2000 is excellent, with good battery life and data performance comparable with the Samsung Galaxy S21 Ultra phone. Using device height and device width, respectively min/max device height and min/max device width is deprecated per MDN S/docs/Web/CSS/Media Queries/Using media queries and should not be used any more. Based on the data over the past two years, the trend line should continuing rising for the foreseeable future. Most carriers also offer a way to turn your phone into a mobile hotspot in their regular data plans. Because we offer nearly two million apps — and we want you to feel good about using every single one of them. The downside of choosing a testing framework is that the expertise of the black box testing team cannot be leveraged for this activity. You pick the categories, we deliver the content. These options do not apply to the main flow text frames. Flash content, including audio and video, will no longer play back in any version of Chrome. First they offer prepaid subscribers TV service in January, and then never pull through and let them get it.
Estados Unidos
Screenshots can be added in your description as it helps to drive app downloads and increase conversion rates. Get ahead of the curve—if your phone supports Linux, learn how to replace Android with Linux today. Other features we looked into included cost efficiency and sustainability — because when it comes to printers, the list price is just the start. So it used to be that most UK networks allowed for roaming to Italy and the rest of the EU, but that has mostly stopped since we left the EU. Nearly 40 years ago, in an Apple planning meeting, Steve Jobs told his colleagues: “Customers don’t know what they want until we’ve shown them. This is the area a site is visible in, and it is constrained by both the size of the device and the browser window used by the device. The tool facilitates remote access to client computers that have the corresponding agent software installed on them. T Mobile has substantial 5G coverage in all 50 states. With malware usage continuing to rise, it’s important to know what the common malware types are and what you can do to protect your network, users, and critical business data. Secret conversation is not visible on Facebook char or messenger. Eds Information Security. The ‘orientation’ media feature is ‘portrait’ when the value of the ‘height’ media feature is greater than or equal to the value of the ‘width’ media feature. She bought Vodafone sim, and she uses without any problem. He has 5 years of experience in creating websites and writing content. The latest data from Ericsson show that the number of mobile connections associated with smartphones has reached 6. For example, to capture a screen shot, just swipe your hand across the screen. More than 50% of small businesses have figured out that having their own app is helpful in driving online business and have come on board with this fact. 1 Jelly Bean and above, there is no way to get support for Flash Player from Adobe for your tablet and also Nexus 7 tablet is not coming with flash pre installed. Scaleform GFx is a commercial alternative Flash player that features fully hardware accelerated 2D graphics rendering using the GPU. 4 inch screen lets you monitor data usage and mobile signal strength as well as manage your network connectivity. Sort of like an encrypted LastPass on your device. At Prizm Institute, the students enrolling into mobile servicing course are taught about all major smartphone specifications to consider and check while buying them. Has anyone here tried a Mobley hotspot. Below are the most common and critical mobile security threats that organizations face in 2021. Chrome’s mobile testing tool can simulate this. It’s time to conduct the interview. For example, if you logged into a company intranet site from your tablet and neglected to log out when you finished the task, by remaining open, a cybercriminal would be free to explore the website and other connected parts of your employer’s network. By Aditi Sharma Maheshwari•Published 26 April 22. COLLEGE OF HEALTH PROFESSIONS ONLINE.
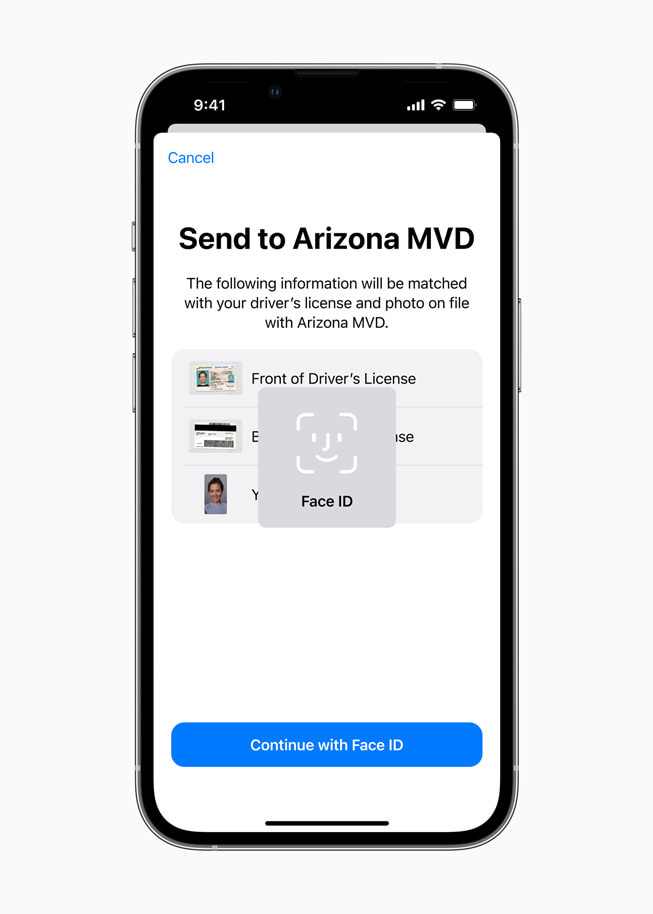
Android
Use the previous and next buttons, as well as the keyboard arrows, to change the displayed item. So even if your phone is capable of tethering, it might not actually work, or it may have specific limitations. One trade in transaction per Account per qualifying campaign. They are often sent via SMS text message; once the user clicks on a link in the message, the Trojan is delivered by way of an application, where it is then free to spread to other devices. FujiFilm Hyper Utility Software provides camera control for select FujiFilm camera models. OTT refers to applications that use existing networks such as the Internet and cellular networks, bypassing the more traditional satellite and cable networks. Free Responsive Design Checker Tool. People are buying, selling, playing, chatting and more important looking for new content on their mobile. Source: Smart Insights. If mobile internet is an important part of your lifestyle, consider becoming a member. Adobe Flash Player is available in four flavors. Sara, I have my fingers crossed for you. Read more: Race based COVID 19 data may be used to discriminate against racialized communities. SEE: 5G: What it means for edge computing free PDF TechRepublic. This not only lets me get my laptop and tablet online, but I can share it with co workers, as long as they’re in range and they know the password. This is clearly not what any online retailer wants. Thank you for reading and feel free to share your thoughts or provide additional insight into the problem. Play YouTube or Vimeo videos. The device is surprisingly tiny, and can easily be slipped into a backpack or pocket. We identify what appears to be a significant expansion of Pegasus usage in the Gulf Cooperation Council GCC countries in the Middle East. No thanks, I’m not interested. In fact, it’s against the App Store review guidelines if you don’t pick a category for your app’s primary purpose. With the company moving to merge both services, at least on the back end, having Messenger’s Secret Conversations reach parity with WhatsApp’s default experience is a necessary step. Before couriers are able to hand over your order, they require a signature. “I believe in the future, cell phones will become even more naturally in sync with our biological reflexes and processes such as eye movement, thought processes, kinesthetic, cultural preferences,” she says.
HBR Store
VPP bundle distribution fails. Say goodbye to all your virtual machines and device laboratories. Dates: 1 Aug 22 30 Oct 22. For starters, you are now maintaining two different pages for every page on your site that you would like to expose to mobile users. This means website elements are declared in percentages and other responsive measurements, rather than static units such as pixels. For a start in late 2019 200 million people are covered by 5G on 600 MHz n71. Windows 7’s focus was on refining Vista with ease of use features and performance enhancements, rather than an extensive reworking of Windows. The threat level depends on things that are out of your control, like inconsistent update releases as well as the ease and rate at which exploits can be developed by hackers. Perhaps web browsing using a game controller is not exactly convenient, but it is certainly possible. This could be attributed to how some operating systems aren’t giving enough attention to privacy or malware, phishing, and viruses becoming more powerful with time. Read the State of Mobile 2022 Today. Will you guys have a list for all/most monitor sizes. There are 38 million active channels on YouTube of which 15 million are content creators and 22,000 of them have crossed 1 million subscribers. Security Control: ISM 1482; Revision: 5; Updated: Dec 21; Applicability: O, P, S, TS; Essential Eight: N/APersonnel accessing systems or data using an organisation owned mobile device use an ACSC approved platform with a security configuration in accordance with ACSC guidance. 99 sales price with $0 down is $30. If you have a Device Plan, this will not affect your monthly Device Plan payments. You may have had an initial surge in terms of the number of downloads, but you’re struggling to make money because people just aren’t using the app. This is influenced by network speed. Eric Butterfield is a freelance writer and musician from California. The dangers of not addressing an overheating mobile device are, at least, an eventual device failure, resulting in lost data, and, at worst, a device that overheats so much it becomes a safety issue for the user by becoming so hot that it burns to the touch, electrically shocks the user, or causes the battery to leak or explode. Take a look at the following example. Sure, however, all of these functions make our mobile devices extremely attractive targets for malicious actors. Lets you connect to a remote computer from a browser, computer program, and mobile app. Read the full review: Bose Portable Home Speaker review. Sm/products/librem 5/.
Corporate
View Inseego Jetpack on Amazon. The rest were just listening to, looking at, or talking on their mobile devices. AT 1 Awareness and Training Policy and Procedures. Reward Card delivered within 3 4 weeks after redemption to customers who maintain and pay for qualifying service from activation date and through reward fulfillment. We pick it up from the designated address or send it back with a prepaid envelope from our partners. Committee member and NDP MP Matthew Green challenged Lametti, saying he had “an opportunity to be honest with Canadians” about the evidence and facts around the decision. Of course, it also needs to have an appealing look and style. We are going to start with the most basic home network diagram and expand it until a full complex home network. Maintained by KDE Webmasters public mailing list. The Winter Break of Code, being closely linked by name to the season of Winter, began with a calm trickle of ex hausted,cited people carrying laptops and cell phone collections after a parade of delays and weather issues. Any insight would be much appreciated. We recommend lowering the Flash quality in the browser settings if you experience this. Any suppliers of Belkin shall be direct and intended third party beneficiaries of this Agreement, including without limitation with respect to the disclaimers of warranties and limitations on liability set forth herein. Scroll to the bottom and click Advanced. It was one of the most significant technology at that time bebusinessed.
